Authentication & SSO¶
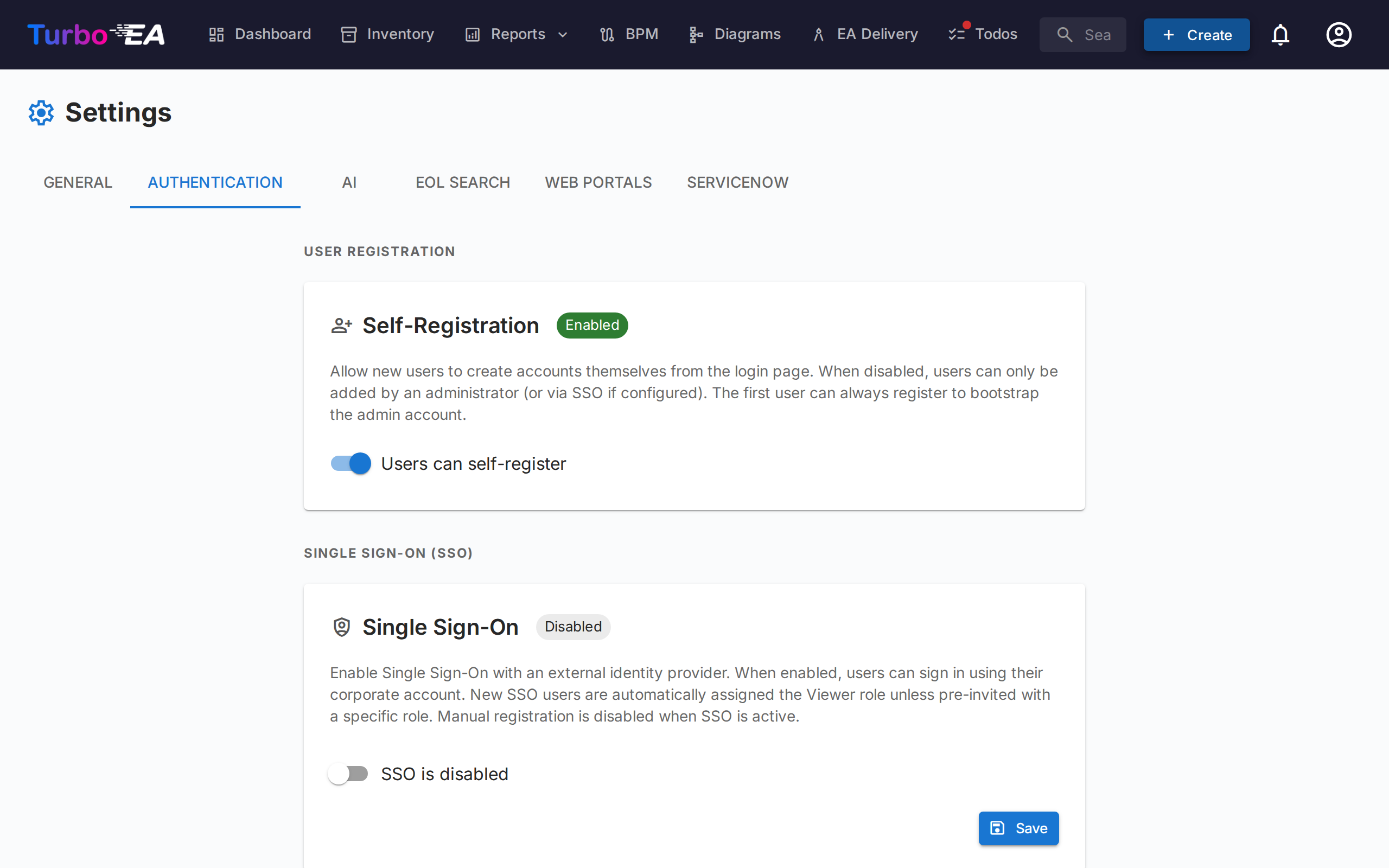
The Authentication tab in Settings allows administrators to configure how users sign in to the platform.
Self-Registration¶
- Allow self-registration: When enabled, new users can create accounts by clicking "Sign Up" on the login page. When disabled, only administrators can create accounts via the Invite User flow.
SSO (Single Sign-On) Configuration¶
SSO allows users to sign in using their corporate identity provider instead of a local password. Turbo EA supports four SSO providers:
| Provider | Description |
|---|---|
| Microsoft Entra ID | For organizations using Microsoft 365 / Azure AD |
| Google Workspace | For organizations using Google Workspace |
| Okta | For organizations using Okta as their identity platform |
| Generic OIDC | For any OpenID Connect-compatible provider (e.g., Authentik, Keycloak, Auth0) |
Steps to configure SSO:
- Go to Admin > Settings > Authentication
- Toggle Enable SSO to on
- Select your SSO Provider from the dropdown
- Enter the required credentials from your identity provider:
- Client ID: The application/client ID from your identity provider
- Client Secret: The application secret (stored encrypted in the database)
- Provider-specific fields:
- Microsoft: Tenant ID (e.g.,
your-tenant-idorcommonfor multi-tenant) - Google: Hosted Domain (optional, restricts login to a specific Google Workspace domain)
- Okta: Okta Domain (e.g.,
your-org.okta.com) - Generic OIDC: Issuer URL (e.g.,
https://auth.example.com/application/o/my-app/). For Generic OIDC, the system attempts auto-discovery via the.well-known/openid-configurationendpoint
- Microsoft: Tenant ID (e.g.,
- Click Save
Manual OIDC Endpoints (Advanced):
If the backend cannot reach your identity provider's discovery document (e.g., due to Docker networking or self-signed certificates), you can manually specify the OIDC endpoints:
- Authorization Endpoint: The URL where users are redirected to authenticate
- Token Endpoint: The URL used to exchange the authorization code for tokens
- JWKS URI: The URL for the JSON Web Key Set used to verify token signatures
These fields are optional. If left blank, the system uses auto-discovery. When filled in, they override the auto-discovered values.
Testing SSO:
After saving, open a new browser tab (or incognito window) and verify that the SSO login button appears on the login page and that authentication works end-to-end.
Important notes:
- The Client Secret is stored encrypted in the database and never exposed in API responses
- When SSO is enabled, local password login remains available as a fallback
- You can configure the redirect URI in your identity provider as: https://your-turbo-ea-domain/auth/callback